Why Blockchain Needs Real Privacy
You've heard about blockchains being "transparent." That sounds good until you realize your financial records live on public ledgers too. What happens when governments demand transaction logs? Or competitors track your NFT purchases? Automata Network is a privacy middleware protocol designed to solve these exact problems using hardware-backed encryption. Launched in 2021, it anchors security in silicon-level trusted execution environments rather than just mathematical algorithms.
Unlike typical crypto projects promising vague improvements, Automata delivers three tangible layers of protection: geographically distributed hardware enclaves, zero-trust network architecture, and verifiable off-chain computation. Its ecosystem includes products like Carrier Bridge - enabling cross-chain asset transfers without metadata leaks and the Witness governance tool that lets DAO members vote privately. Now let's break down why this matters.
Core Technology Deep Dive
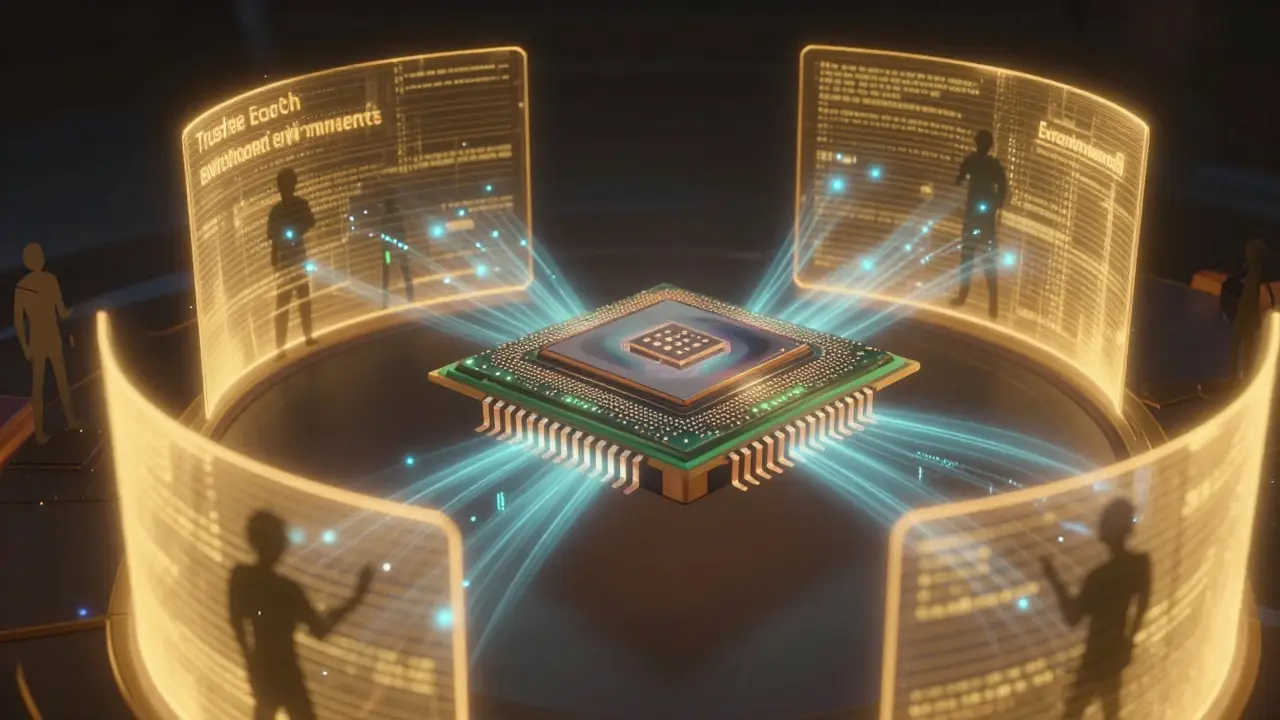
The magic happens in Trusted Execution Environments (TEEs) - specialized processor zones physically isolated from regular memory spaces. Automata uses Intel SGX processors globally, creating air-gapped computing cells where even admins can't peek inside encrypted operations. This differs from software-only approaches because physical hardware controls access.
| Feature | Traditional Blockchains | Automata Solution |
|---|---|---|
| Data Protection | Pseudo-anonymous addresses | TEE-isolated computations |
| Voting Systems | Public ballots expose choices | Automata Witness enables secret ballots |
| Cross-Chain Risks | RWA bridges leak metadata | Carrier relays hide transaction paths |
Another game-changer is Oblivious RAM - preventing system operators from seeing which files get accessed. Combined with zero-knowledge proofs, this stops hackers from inferring patterns even when they intercept network traffic. Remember when Silk Road tried similar concepts? Their servers were vulnerable because encryption lived only in code. Hardware roots remove human error vectors entirely.
Ecosystem Components Breakdown
Three workhorse products drive the platform:
- Geode Providers: Renting encrypted compute space via auction mechanism. Think cloud services where AWS can't spy on your data processing jobs
- Attestor Nodes: Validating whether remote processes match intended logic. Critical for smart contracts executing sensitive functions like identity verification
- Validator Council: Decentralized group auditing security compliance across geographic TEE clusters
These form interlocking layers. If Validator Nodes detect irregularities in Attestor reports, the Control Plane automatically reconfigures affected Service Nodes before breaches occur. It's cybersecurity automation meeting Byzantine fault tolerance principles.
Token Economics Simplified
The ATA token operates under two critical frameworks: utility and governance. Total supply fixed at 1 billion, with 488.5 million circulating as of April 2024 according to CoinMarketCap archives. Notable allocation breakdowns:
- Protocol Fees - Paying storage/compute services in ATA creates direct economic pressure proportional to usage
- Governance Voting - Token weighting determines parameter updates like fee structures or validator thresholds
- Staking Incentives - Locking ATA rewards holders based on duration commitment, balancing inflation against participation depth
Compare this to ETH gas models where fees vanish through burning. Here payments flow directly back into liquidity pools maintaining operational stability. Early Binance Launchpool participants raised $2.4M pre-IPO in June 2021, demonstrating institutional validation despite later volatility hitting lows near $1.37 after initial spikes.
Real-World Usage Scenarios
Consider Jane, an art collector bidding on digital sculptures stored on Ethereum. She fears competitors monitoring her wallet activity. Using Carrier Bridge, she can transfer assets between chains while obscuring recipient addresses through homomorphic encryption techniques. Meanwhile, her local city council adopts Automata Witness for budget votes - citizens register preferences anonymously yet prove eligibility through zk-proofs.
Enterprise users benefit differently. Healthcare providers storing patient records on IPFS gain extra insurance when Automata seals access permissions within hardware enclaves. Even regulators approve such systems since decryption keys never leave protected zones. Compare this to standard blockchain solutions requiring manual audits annually versus continuous cryptographic guarantees here.

Current Market Position & Challenges
Despite technological strengths, adoption hurdles persist. Regulatory scrutiny around hardware enclaves varies globally - Singapore grants exemptions while EU GDPR imposes stricter documentation demands. Transaction costs remain higher than Layer-2 alternatives though security premium justifies pricing according to Chainalysis Enterprise reports from 2025.
| Privacy Tool | Speed | Cost Efficiency | Adoption Barrier |
|---|---|---|---|
| ZK-SNARK Rollups | Fast | Low fees | Requires heavy math understanding |
| Mixers | Slow batch times | High operational cost | Limited jurisdiction acceptance |
| Automata | Moderate throughput | Premium pricing | Huge developer community growth potential |
FAQ Section
Can I mine Automata Network tokens?
No - Proof-of-Stake consensus requires locking existing ATA coins instead of mining new units. Staking durations affect reward rates linearly.
How does Carrier Bridge protect my data?
It encrypts all routing information inside Intel SGX enclaves, making packet inspection impossible even for service providers handling requests.
What makes ATA different from Monero?
Monero focuses solely on coin confidentiality; Automata secures entire application workflows including smart contract executions and cross-platform data flows.
Are there any known security vulnerabilities?
While no major exploits occurred since launch, researchers identified theoretical attack vectors involving side-channel timing attacks mitigated in Q3 2025 firmware updates.
Should long-term investors stake their holdings?
Yes - annual returns averaged 7-9% APY in 2024, plus increased governance influence. Consider unclaimable penalties if early withdrawals interrupt lock periods.







Write a comment